As with all forms of security testing, API security testing focuses its relevance on the importance of data to an organization. Threat recognition at the right time makes the difference between a secured API and severe data loss.
API security testing ensures that all such threats and errors are discovered and resolved for subsequent security of applications that use API.
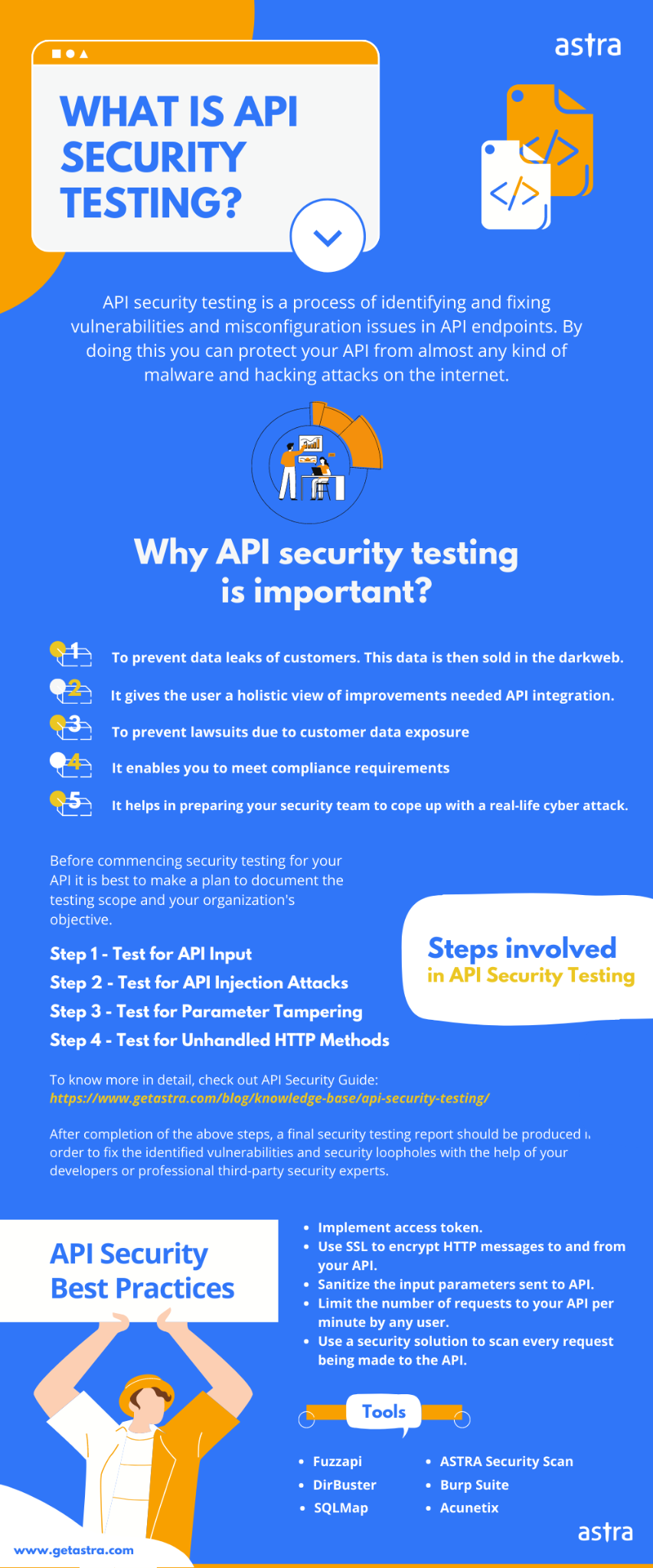
Methods of API Security Testing
Here are some verified methods of the API security testing process to ensure compliance to certain safety regulations and allow for optimized performance:
1. Fuzz Testing
A black-box software testing technique, fuzz testing detects the vulnerabilities and hidden bugs using specially designed data injection attacks. The advantage of fuzz testing lies in its lack of use of advanced tools and the ability to be performed on any application.
A majority of the fuzz testing happens by sending unapproved data to the input fields to check if the API breaks and allows for a hacking opportunity. For example, fuzz testing through numbers happens when negative digits, zero, or large numbers are sent to the API to detect bugs in the coding. With strings, one can try and send SQL queries instead of the expected value of a different type with the expectation that the query will not be implemented.
2. Unauthorized endpoints and methods
All requests sent via the API should be authorized accordingly before being implemented to ensure that they aren’t hidden attempts at accessing sensitive data. If such a check isn’t done, users may cause accidental data leakages or hackers can immediately access the data with a suitably modified query. This can also be considered as a part of pentesting for API endpoints.
3. Unhandled HTTP methods
When an API uses HTTP, there are various methods for retrieving the data or using different functions related to it, such as saving or deleting. In this case, API security testing should set up specific scenarios that use the HEAD technique to escape the authentication process and test different methods based on HTTP.
4. Command injection flaws
Injection attacks usually take place when there’s an interaction between the web services and the API and there’s a transfer of information through the HTTP request. This happens through commands such as those related to the database, requests for external services, or system calls. Lack of proper data validation techniques means the API will implement commands without verifying their impact on the system (data loss or wiping out the entire contents of the server).
For example, API requests can be operating system commands based on the OS it runs on (Linux, Windows, etc.). Even with a simple request to delete a file by name, if the name of the file is modified to be a malicious attack by the hacker, it can cause unwanted execution and complications.
SQL injection attacks may also arise from a lack of data validation used in API requests. It will lead to hackers accessing the database through carefully designed commands and planting malware or deletion of important files.
5. Authenticating Endpoints
As we read before, authorization at every endpoint is very important for API security. API security testing should design strategies that may compromise sensitive data of the organization and verify the authorization levels at each endpoint and the privileges granted for each user.
6. Parameter manipulation
The parameters sent through API requests can be tampered with by disguising errors sent through the backend. For example, any forms that use ‘hidden’ input should be verified to ensure that it’s validated in the right manner by the backend server.
Tools for API Security Testing
Now that we’ve gone through the various methods involved in API security testing, here’s a brief overview of the tools available for the implementation of these security strategies:
- Katalon Studio
A free security testing tool for a variety of applications, this tool allows the user to test both REST and SOAP API requests, along with different commands and associated functions. Its special characteristic involves the combination of UI and API so that multiple environments can be tested.
- Postman
This tool specializes in sending specific HTTP requests and offers security testing for web services and API on Mac and Windows. Other features include a well-developed interface, features for running, testing, documenting, and supervision, and the ability to conduct both automated and manual testing.
- SoapUI
SoapUI leans more towards API security testing with tests designed for REST, SOAP APIs and other web services. Special features include the quick running of tests, security scanning, and load tests for functional testing.
- Tricentis Tosca
Known for its continuous security testing platform, it allows for tests of various protocols such as SOAP, Rabbit MQ, IBM MQ, etc. Its versatility is useful for testing across packaged apps, mobiles, etc.
These are a few of the methods and tools used commonly in API security testing methods. Often, the best strategy for tackling API-related issues is to keep aware of the latest developments, remain vigilant, and conduct web app pentesting procedures.